Hilfe
3-DES
Der symmetrische, kryptographische Verschlüsselungsalgorithmus 3-DES (Triple-DES) ist eine Weiterentwicklung des Data Encryption Standard DES und verwendet symmetrische Schlüssel der Länge 112 Bit. Der DES ist ein weit verbreiteter Verschlüsselungsalgorithmus mit einer verwendeten Schlüssellänge von 56 Bit. Diese Schlüssellänge wird jedoch heute als unsicher angesehen. Beim 3-DES wird die DES Verschlüsselung dreimal hintereinander mit zwei unabhängigen kryptographischen Schlüsseln durchgeführt, die aus dem 112 Bit Schlüssel generiert werden. DES ist als Federal Information Processing Standard FIPS 46-3 standardisiert und wird durch ANSI X9.52-1998 zum 3-DES.
A
Advanced Encryption Standard (AES)
Der Advanced Encryption Standard AES ist ein symmetrischer Verschlüsselungsalgorithmus, der mit symmetrischen Schlüsseln der Länge 128, 192 und 256 Bit operieren kann. Er wurde von den Kryptographen Dr. Joan Daemen und Dr. Vincent Rijmen unter dem Namen Rijndael-Chiffre entwickelt. Der Algorithmus wird für das 21. Jahrhundert als ausreichend sicher angesehen. Er wurde im Jahr 2001 als Federal Information Processing Standard FIPS 197 standardisiert.
Aktivierungs-Code
Der Aktivierungs-Code ist ein von der Finanzverwaltung generierter, 12-stelliger alphanumerischer Wert, der dem Anwender einmalig zur Aktivierung seiner Login-Option zu Mein ELSTER dient. Er kann effektiv nur in Kombination mit einer dazugehörigen Aktivierungs-ID verwendet werden. Der individuelle Aktivierungs-Code wird Ihnen bei der Registrierung auf dem Postweg mitgeteilt.
Aktivierungsdaten
Aktivierungsdaten dienen einem Anwender von Mein ELSTER dazu, seine Login-Option zu aktivieren. Die Aktivierungsdaten bestehen aus dem Aktivierungs-Code und der Aktivierungs-ID, die der Anwender von der Finanzverwaltung übermittelt bekommt.
Aktivierungs-ID
Die Aktivierungs-ID ist eine von der Finanzverwaltung generierte Zahl mit bis zu 20 Stellen, welche dem Anwender zur Aktivierung seiner Login-Option zu Mein ELSTER dient. Sie kann effektiv nur in Kombination mit einem zugehörigen Aktivierungs-Code verwendet werden. Die individuelle Aktivierungs-ID wird Ihnen bei der Registrierung per E-Mail zugestellt.
Asymmetrisches Schlüsselpaar
Ein asymmetrisches Schlüsselpaar ist individuell einem Anwender oder System zugeordnet. Es besteht aus einem öffentlichen Schlüssel und einem privaten (=geheimen) Schlüssel. Der private Schlüssel darf nur dem Inhaber bekannt sein und dient zur individuellen Authentfizierung oder Entschlüsselung elektronischer Informationen mittels asymmetrischer, kryptographischer Verfahren. Der öffentliche Schlüssel dient der Allgemeinheit zur Verifizierung einer mit dem privaten Schlüssel durchgeführten elektronischen Signatur oder zur individuellen Verschlüsselung. Das kryptographische Verfahren stellt sicher, dass Verschlüsselung und Entschlüsselung sowie Signatur und Signaturprüfung beziehungsweise Authentifizierung nur mit dem entsprechenden Schlüsselpaar funktionieren.
Asymmetrische kryptographische Verfahren
Bei asymmetrischen kryptographischen Verfahren bekommt eine Person oder ein System immer zwei Schlüssel, das heißt ein asymmetrisches Schlüsselpaar für zum Beispiel Signatur-, Authentifizierungs- oder Verschlüsselungs funktionen zugewiesen, und zwar einen öffentlichen und einen privaten Schlüssel. Der öffentliche Schlüssel ist jedem zugänglich, der private Schlüssel nur der jeweiligen Person beziehungsweise dem jeweiligen System. Mit dem privaten Schlüssel können Daten zum Beispiel signiert oder authentifiziert und von jedem mit dem zugehörigen, öffentlichen Schlüssel geprüft werden. Außerdem können mit dem öffentlichen Schlüssel Daten für den entsprechenden Kommunikationspartner verschlüsselt und nur mit dessen privaten Schlüssel entschlüsselt werden. Bekannte asymmetrische, kryptographische Verfahren sind zum Beispiel RSA, DSS und ECC.
Authentifizierung
Authentifizierung ist der Vorgang, eine behauptete Identität, beispielsweise eine Person in Bezug zu einer elektronischen Kennung nachzuweisen. Meistens erfolgt der Nachweis bei IT-Systemen mittels Prüfung einer Benutzerkennung und eines Passwortes. Stärkere Sicherheit bietet die Authentifizierung mit asymmetrischen kryptographischen Verfahren oder biometrischen Merkmalen (zum Beispiel Fingerabdruck).
Authentifizierungsmittel
Die Sicherheit von ELSTER beruht unter anderem auf der Verwendung von digitalen Zertifikaten und den dazugehörigen Schlüsselpaaren. Diese Zertifikate und Schlüsselpaare werden entweder in einer Datei oder in einem Chip gespeichert aufbewahrt. Das Medium, auf dem sich diese Zertifikate und Schlüssel befinden, wird Authentifizierungsmittel genannt. Es können folgende Authentifizierungsmittel bei ELSTER verwendet werden:
- Zertifikatsdatei
- Sicherheitsstick
- Signaturkarte
Authentizität
Unter Authentizität wird allgemein die Echtheit (Unverfälschtheit) und Glaubwürdigkeit von Daten oder einer Partnerinstanz verstanden. Die Authentizität kann durch kryptographische Verfahren, z. B. über asymmetrischen kryptographischen Verfahren gesichert und überprüft werden.
B
Benutzername
Der Benutzername ist in Mein ELSTER eine elektronische Identität eines Benutzerkontos. Unter einem Benutzernamen kann eine frei wählbare Zeichenfolge (maximal 8 Zeichen) verwendet werden. Er dient dazu, mehrere persönliche Zugangsmöglichkeiten in Mein ELSTER zu unterscheiden, falls ein Anwender sich mehrfach registriert. Da bei der ersten Registrierung noch nicht feststeht, ob später weitere persönliche Zugangsmöglichkeiten vom Anwender gewünscht werden, muss bei jeder Registrierung ein Benutzername vergeben werden.
Bescheinigung
Als Bescheinigungen werden folgende elektronische Daten, die der Steuerverwaltung zu Ihrer Person übermittelt wurden, bezeichnet:
- vom Arbeitgeber übermittelte Lohnsteuerbescheinigungen
- Lohnersatzleistungen (zum Beispiel Arbeitslosengeld, Krankengeld, Elterngeld)
- Mitteilungen über den Bezug von Rentenleistungen
- Beiträge zu Kranken- und Pflegeversicherungen
- Vorsorgeaufwendungen (zum Beispiel Riester- oder Rürup-Verträge)
- Beiträge für Vermögenswirksame Leistungen (VWL / VL)
Die Steuerverwaltung sammelt diese Daten und stellt sie Ihnen zum Abruf zur Verfügung. Sie (oder ein von Ihnen Bevollmächtigter, z. B. Ihr Steuerberater) können so auf die zu Ihrer Person bei der Steuerverwaltung gespeicherten Informationen zugreifen und diese gegebenenfalls für Ihre Einkommensteuererklärung verwenden.
BOP
Über das BZStOnline-Portal (BOP)
stellt das Bundeszentralamt für Steuern (BZSt) elektronische Formulare zur Datenübermittlung für verschiedene Verfahren im Verantwortungsbereich des BZSt zur Verfügung, beispielsweise zur Kirchensteuer, Versicherungs- und Feuerschutzsteuer oder Vorsteuervergütung. Eine vollständige Auflistung der angebotenen Formulare liefert die entsprechende Übersichtsseite des BOP.
C
Common Criteria
Kriterien für die Prüfung und Bewertung der Sicherheit von Informationstechnik. Sie sind für die Bewertung der Sicherheitseigenschaften praktisch aller informationstechnischen Produkte und Systeme geeignet. Durch die internationale Standardisierungsorganisation (ISO) sind sie unter der Nummer 15408 als internationaler Standard aufgenommen.
Computerviren
In der Fachsprache ist ein Computervirus eine nichtselbständige Programmroutine, die sich selbst reproduziert, indem sie sich an andere Software oder Bereiche des Betriebssystems zum Beispiel eines Computers anhängt und, einmal gestartet, vom Anwender nicht kontrollierbare Manipulationen an selbigen vornimmt. Die Idee zu Computerviren leitete sich von dem biologischen Vorbild der Viren ab und gab ihnen ihren Namen. Durch Computerviren kommt es auf einem Computer häufig zur Veränderung oder Verlust von Daten und Programmen sowie zu Störungen des regulären Betriebs.
D
Dokumententyp
In Mein ELSTER kann die Registrierung mit dem neuen Personalausweis (nPA) oder mit dem elektronischen Aufenthaltstitel (eAT) durchgeführt werden. Anhand des Attributs "Dokumententyp" sind die beiden unterschiedlichen Ausweisetypen technisch unterscheidbar. Der Dokumententyp ist „ID" beim nPA und „AR", „AS" oder „AF" beim eAT.
E
Elektronische Identität
Die elektronische Identität ist ein für ein System nachvollziehbarer Name, dem es eine Person oder ein anderes System zuordnen kann. Oftmals wird dieser Name als Benutzerkennung oder Account bezeichnet. Einer elektronischen Identität sind auf einem System Rechte zugewiesen, welche die Nutzung des Systems eingrenzen. Dies soll sicherstellen, dass der Anwender wirklich der legitime Nutzer der entsprechenden Identität ist. Dies geschieht durch einen sicheren Authentifizierung sprozess.
Elektronische Signatur
Eine elektronische Signatur ist ein technisches Verfahren. Mit der elektronischen Signatur kann der Urheber von Daten ermittelt werden. Sie kann auf dem elektronischen Weg für eine Willenserklärung oder zur Authentifizierung verwendet werden. Zur Erzeugung und Überprüfung von elektronischen Signaturen können asymmetrischen kryptographischen Verfahren verwendet werden.
Bei Elster wird die elektronische Signatur ausschliesslich zur Authentifizierung verwendet (Authentifizierungs-Signatur).
Elektronischer Missbrauch
Unter elektronischem Missbrauch versteht man den unberechtigten Zugriff auf Systeme inklusive der unberechtigten Nutzung der Systeme für eigene Zwecke. Es ist zu beachten, dass in Deutschland bereits der unberechtigte Zugriff auf einen fremden Computer strafbar ist. Gesetze über den Computermissbrauch sind in der EU nicht einheitlich geregelt.
ELSTER-Funktionsbibliothek
Bezeichnet eine Software beziehungsweise eine Datei der Finanzverwaltung, welche vordefinierte Funktionen für den technischen Zugang eines Computers auf Mein ELSTER zur Einbindung in andere Computer-Software bereithält.
ELSTER-SSL-Zertifikat
Das SSL-Zertifikat von ELSTER ist von einem international anerkannten Trustcenter ausgestellt (zum Beispiel Verisign, Symantec Corporation, Thawte oder TC-Trustcenter) und dient der Beglaubigung der Identität von Mein ELSTER gegenüber einem Computer beziehungsweise einem Anwender. Das Zertifikat besitzt ein eindeutiges Merkmal. Dies ist sein elektronischer SHA1-Fingerabdruck, der lautet: 52 EA E1 6F 40 64 38 B7 FF 02 91 C1 7D 36 82 DD 9B 41 7A 90. Sollte ein Zertifikat einen anderen Fingerabdruck haben, so ist es nicht das ELSTER-SSL-Zertifikat.
ELSTER-Policy
Signaturerzeugungskomponenten (zum Beispiel Signaturkarten) und Zertifizierungsdiensteanbieter (zum Beispiel Trustcenter), die im Zusammenhang mit der elektronischen Steuererklärung in Mein ELSTER und weiteren zugehörigen Diensten eingesetzt werden sollen, müssen sicherheitstechnisch einen gewissen Mindeststandard besitzen und einigen technischen Anforderungen genügen. Der sicherheitstechnische Mindeststandard und die technischen Anforderungen werden in der ELSTER-Policy der Finanzverwaltung beschrieben.
F
Fortgeschrittene Signaturkarte
Die auf einer fortgeschrittenen Signaturkarte enthaltenen asymmetrischen Schlüsselpaare sind durch anerkannte Trustcenter oder durch Vertragsbeziehungen eindeutig einem Inhaber zugeordnet und gemäß international anerkannten Richtlinien generiert. Sie ermöglichen dem Inhaber elektronische Signaturen zu erstellen, welche eindeutig die Identifizierung der Signatur für andere ermöglichen. Die Signaturkarte ist dem Inhaber persönlich zugeordnet und muss unter seiner Kontrolle sein.
Freischaltcode
Der Freischaltcode kommt zum Einsatz bei der Genehmigung des Antrags einer anderen Person, wenn diese Person, deren Bescheinigungen abgerufen werden sollen, keine Registrierung bei Mein ELSTER mit Identifikationsnummer durchgeführt oder sich noch nicht zum Abruf von Bescheinigungen angemeldet hat. Der Freischaltcode wird per Post an die Person, deren Bescheinigungen Sie abrufen möchten, versendet. Der 12-stellige Code ist ein Einmalcode, der nur für die Genehmigung eines Antrags gültig ist. Der Empfänger kann nach Erhalt des Briefes entscheiden, ob er den Code an den Antragsteller weitergibt und diesem dadurch den Abruf seiner Bescheinigungen ermöglicht. Der Freischaltcode verfällt automatisch, wenn er nicht innerhalb von 90 Tagen an den Antragsteller weitergegeben und verwendet wird.
H
Hacker
Als Hacker werden Personen bezeichnet, die in fremde Netzwerke, Datenbanken oder Festplatten eindringen, um dort enthaltene Daten zu stehlen oder um an persönliche Informationen zu kommen. Sie dringen zumeist ohne Wissen des Opfers ein, um Schlüsselmittel, Kontonummern oder Kreditkartennummern in Erfahrung zu bringen.
Hijacking
Als Hijacking wird die unerlaubte Übernahme einer Kommunikationsverbindung zwischen einem Computer und einem Server bezeichnet. Damit ein Angreifer eine Kommunikationsverbindung übernehmen kann, hört er sämtliche Daten einer fremden Onlinesitzung ab. Mithilfe der gesammelten Daten erhält der Angreifer gegebenenfalls genug Informationen, um eine Synchronisation seines Computers mit dem in Frage kommenden Server zu erreichen. Der Server merkt dabei nicht, dass er mit einem anderen, als dem bekannten Computer, der die Kommunikationsverbindung aufgebaut hat, verbunden ist. Durch Hijacking kann es möglich sein, authentifizierte Kommunikationsverbindungen zu übernehmen, wenn die Kommunikationsverbindung nicht ausreichend abgesichert ist.
Hardware Security Modul (HSM)
Der Begriff Hardware-Sicherheitsmodul (HSM) oder englisch Hardware Security Module bezeichnet ein (internes oder externes) Peripheriegerät für die effiziente und sichere Ausführung kryptographischer Operationen. Somit ermöglicht es, die Vertrauenswürdigkeit und die Integrität von Daten und den damit verbundenen Informationen in geschäftskritischen IT-Systemen sicherzustellen. Um die Vertrauenswürdigkeit zu gewährleisten, müssen die zum Einsatz kommenden kryptographischen Schlüssel sowohl softwaretechnisch als auch gegen physikalische Angriffe oder Seitenkanalangriffe geschützt werden.
HTML-Seite
Eine HTML-Seite ist eine Internet-Seite, die mit der Hyper-Text-Markup-Language entwickelt beziehungsweise geschrieben wurde. Traditionell wird zur Herstellung von Internet-Seiten HMTL benutzt.
HTTPS
HTTPS ist die Sicherheitsvariante des Internet-Protokolls HTTP (Hyper-Text-Transfer-Protokoll) zur Übertragung von Informationen über das Internet. Es bindet das Sicherheitsprotokoll TLS ein, welches Verschlüsselungs- und Authentifizierungs mechanismen für eine Kommunikationsverbindung über Internet bietet.
Hybrider kryptographischer Algorithmus
Stellt ein kryptographisches Verfahren dar, welches symmetrische und asymmetrische Verfahren kombiniert. Zumeist werden dabei symmetrische Verfahren als Verschlüsselungsmechanismen eingesetzt und die asymmetrischen Verfahren als Schlüsselaustauschmethoden verwendet (Verschlüsselung der symmetrischen Schlüssel mit dem öffentlichen Schlüssel des Empfängers).
I
Identifikationsnummer
Ihre persönliche Identifikationsnummer finden Sie im Kopfbereich von jedem Anschreiben Ihres Finanzamtes.
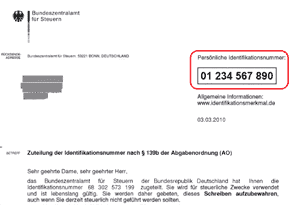
Falls Sie Ihre persönliche Identifikationsnummer noch nicht erhalten haben oder sie verlegt haben, können Sie diese beim Bundeszentralamt für Steuern anfordern.
Integrität
Integrität ist auf dem Gebiet der Informationssicherheit ein Schutzziel, das besagt, dass Daten über einen bestimmten Zeitraum vollständig und unverändert sein sollen. Eine Veränderung könnte absichtlich, unabsichtlich oder durch einen technischen Fehler auftreten. Integrität umfasst also Datensicherheit (Schutz vor Verlust) und Fälschungssicherheit (Schutz vor vorsätzlicher Veränderung).
Die Integrität von Daten ist gewährleistet, wenn die Daten vom angegebenen Absender stammen und vollständig sowie unverändert an den Empfänger übertragen worden sind.
ITSec
Die Evaluierung nach ITSec beinhaltet die Prüfung und Bewertung der Sicherheitseigenschaften eines informationstechnischen Produkts nach festgelegten Sicherheitskriterien, angeleitet durch ein Evaluationshandbuch. Sie geht über eine einfache Konformitätsprüfung zwischen einem Benutzerhandbuch und tatsächlichem Verhalten des Produkts weit hinaus.
J
Java-Applet
Ein Java-Applet ist eine in der Programmiersprache Java geschriebene Anwendung, die innerhalb eines Internet-Browsers ausgeführt werden kann. Es bietet die Möglichkeit der Computer-seitigen Datenverarbeitung von aktiven Web-Inhalten in einer Internet-basierten Computer/Server Umgebung. Das Java-Applet wird dabei nach Erfordernis automatisch vom Server in den Internet-Browser des Computers geladen. Seit Juli 2017 werden in Mein ELSTER keine Java-Applets mehr verwendet.
K
Kryptoboxen
Kryptoboxen dienen in der Regel einer generellen Verschlüsselung von Kommunikationsverbindungen beziehungsweise einer Leitungsverschlüsselung. Alle elektronischen Informationen, die über eine Kommunikationsverbindung gesendet werden, werden auf der einen Seite in einem Knotenpunkt durch eine Kryptobox verschlüsselt und auf der anderen Seite wieder in einem Knotenpunkt durch eine andere Kryptobox entschlüsselt. Im Allgemeinen basiert die Sicherheit der Leitungsverschlüsslung auf starken symmetrischen kryptographischen Verfahren. Alle elektronischen Informationen werden dabei mit dem gleichen symmetrischen Schlüssel verschlüsselt, der nur den relevanten Kryptoboxen bekannt ist.
Kryptochip
Ein Kryptochip ist ein hochleistungsfähiger Prozessor, der kryptographische Operationen beschleunigt und sicher durchführen kann. Er ermöglicht die sichere Speicherung von persönlichen Schlüsselmitteln, um diese vor unberechtigtem Zugriff zu schützen. Zum Beispiel ermöglicht er im Rahmen der asymmetrischen kryptographischen Verfahren die individuelle sichere Speicherung von privaten Schlüsseln. Als Ausprägung kann ein Kryptochip in Chipkarten oder in Computersystemen verwendet werden.
Kryptographie
Originäres Ziel der Kryptografie ist das Unkenntlichmachen von Daten für unberechtigte Dritte durch Anwenden von Verschlüsselungs methoden, beziehungsweise die Lehre von der Geheimhaltung von Informationen. Die Verschlüsselung gilt als umso stärker, je mehr theoretischer beziehungsweise mathematischer Aufwand betrieben werden müsste, um die Rekonstruktion der Daten durch einen Unbefugten durchzuführen. Zur Kryptographie zählen auch Methoden der Authentifizierung, der elektronischen Signatur und des Authentizitäts nachweises.
Kryptomittel
Kryptomittel bezeichnen kryptographische Informationen, die als Eingabe den kryptographischen Verfahren zur Verschlüsselung, Authentifizierung und elektronischen Signatur dienen. Zumeist sind dies individuell von einer Person oder einem System geheim gehaltene Informationen, wie zum Beispiel ein Passwort, eine PIN oder auch der private Schlüssel eines asymmetrischen Schlüsselpaares. Es können auch einzigartige, biometrische Merkmale einer Person sein, wie zum Beispiel ein Fingerabdruck, Eigenschaften der Stimme oder der Augen. Es gibt auch öffentlich bekannte Schlüsselmittel von Personen oder Systemen, die zum Beispiel der Prüfung elektronischer Signaturen beziehungsweise Authentifizierung dienen, wie zum Beispiel der öffentliche Schlüssel eines asymmetrischen Schlüsselpaares.
M
Malware
Mit Malware bezeichnet man jegliche Art bösartiger Software wie Computerviren, Trojaner, Würmer, etc. Sie enthält für den Anwender nicht erkennbare Funktionen, mit denen z.B. Daten gelöscht, verändert oder kopiert werden können. Außerdem können Daten wie Passwörter ausgespäht werden
Masquerading
Masquerading bezeichnet den Sachverhalt, wenn eine Person oder ein System im elektronischen Verkehr eine falsche Identität vortäuscht beziehungsweise es nicht die Identität ist, für die es sich auf elektronischem Weg ausgibt. Unter anderem durch die Ausnutzung von Namensähnlichkeiten oder durch verdeckte elektronische Umleitungen könnte sich zum Beispiel ohne angemessene Sicherheitsvorkehrungen ein fremder Server mit der Internet-Seite eines vertrauten Servers auf einem Computer melden, welche der Anwender aufgerufen hat. Damit könnte der fremde Server zum Beispiel bei einem Login-Versuch des Anwenders ein Passwort ausspionieren oder Dateien entgegen nehmen, die nicht für ihn bestimmt sind, beziehungsweise Daten präsentieren, die nicht vom Original-Server kommen.
Mindestschlüssellänge
Eine Beurteilungsmöglichkeit für die Stärke kryptographischer Verschlüsselungs - und Signaturverfahren ist die Länge der innerhalb der Verfahren einsetzbaren, kryptographischen Schlüssel in Bits gemessen. Je höher die Anzahl der Bits der eingesetzten Schlüssel, umso stärker wird das kryptographische Verfahren beurteilt. Die Mindestschlüssellänge bezeichnet die minimal einzusetzende Anzahl an Bits eines kryptographischen Schlüssels, damit das entsprechende Verfahren noch als stark anzusehen ist.
O
Öffentlicher Schlüssel
Das ist der bei asymmetrischen Verfahren verwendete kryptographische Schlüssel, der vom Eigentümer oder dem ausstellenden Trustcenter öffentlich zugänglich gemacht wird, zum Beispiel über einen Verzeichnisdienst aber auch per Diskette, Internet-Download oder per E-Mail. Mit Hilfe eines von einem Trustcenter ausgestellten und entsprechend elektronisch signierten Zertifikats wird der öffentliche Schlüssel offiziell beglaubigt beziehungsweise zu einer identifizierten Person beziehungsweise einem identifizierten System als zweifelsfrei zugehörig ausgewiesen. Der öffentliche Schlüssel dient der Prüfung elektronischer Signaturen des Eigentümers oder der Verschlüsselung elektronischer Informationen, die nur der Eigentümer mit seinem zugehörigen, privaten Schlüssel entschlüsseln kann.
P
Personal-Firewall
Eine Personal Firewall ist eine Sicherheitssoftware für den persönlichen Computer, um den Zugriffsschutz für Unberechtigte aus dem Internet verstärkt abzusichern. Sie soll den Computer vor Angriffen von außen schützen und auch verhindern, dass bestimmte Programme, zum Beispiel Computerviren, Kontakt vom Computer zum Internet herstellen. Dazu kontrolliert sie alle Verbindungen in andere Netzwerke und überprüft sowohl die Anfragen ins Internet als auch die Daten, die zum Computer kommen.
Phishing
Phishing ist ein vorsätzlicher Angriff eines Hackers mit dem Ziel, persönliche Informationen wie Kreditkartennummern, Passwörter oder PIN-Nummern des Opfers zu erfahren. Das Opfer erhält zum Beispiel eine seriös erscheinende E-Mail oder Internet-Seite von einem scheinbar bekannten Absender wie einer Behörde, Bank oder einem Kreditinstitut. Darin wird das Opfer aufgefordert, eine Internet-Seite zu besuchen und dort aufgrund eines nötigen Abgleichs oder einer Überprüfung oder dergleichen, die geheimen, persönlichen Informationen einzugeben. Da diese Internet-Seite gefälscht ist, erhält der Hacker Zugriff auf die persönlichen Informationen und kann diese für eigene Interessen nutzen.
Phishing ist eine Wortschöpfung aus "Password" und "fishing".
PKCS#12
Defacto Standard der Firma RSA Security, welcher das Format für die Speicherung und den Transport asymmetrischer Schlüsselpaare, entsprechender Zertifikate und weiterer elektronischer Schlüsselmittel definiert.
PKI
Eine Sicherheitsinfrastruktur, die es ermöglicht, in nicht gesicherten Netzen (zum Beispiel Internet) auf der Basis eines von einer vertrauenswürdigen Stelle ausgegebenen Schlüsselpaares (asymmetrische Verschlüsselung) verschlüsselt Daten auszutauschen beziehungsweise Signaturen zu erzeugen und zu prüfen. Weitere Informationen zu asymmetrischer Verschlüsselung beziehungsweise Signaturen finden Sie auf den Seiten des Bundesamtes für Sicherheit in der Informationstechnik (BSI).
Plausibilität
Plausibilität bezeichnet die syntaktische und semantische beziehungsweise die formale und inhaltliche Korrektheit elektronischer Informationen. In Mein ELSTER werden zum Beispiel nur plausible Informationen an die Landesbehörden weiter geleitet.
Privater Schlüssel
Dies ist der bei asymmetrischen Verfahren verwendete kryptographische Schlüssel, auf den nur der Inhaber Zugriff haben darf. Der private Schlüssel dient zur Erzeugung von elektronischen Signaturen (Authentifizierungs-Signaturen) und zur Entschlüsselung von Daten.
PSE
PSE steht für Personal Security Environment. Das ist ein persönlicher, elektronischer Sicherheitsbereich, in dem sicherheitsrelevante Daten, wie beispielsweise ein privater Schlüssel, enthalten sind. Zu finden ist ein PSE in der Regel auf einer Chipkarte, kann aber auch als verschlüsselte Datei vorliegen. Der PSE ist durch ein Passwort, eine PIN oder durch biometrische Verfahren (zum Beispiel Fingerabdruck) gesichert.
Pseudonym
Das Pseudonym, auch abgeleitete Ausweisnummer genannt, dient der Identifikation des Ausweisinhabers, ohne dass personenbezogene Daten über das Internet übertragen werden müssen. Im neuen Personalausweis (nPA) ist eine Pseudonymfunktion integriert. Für jeden Diensteanbieter (z. B.: Mein ELSTER) generiert der Personalausweis ein eigenes Pseudonym, sodass zwei verschiedene Diensteanbieter nicht die gleiche Person anhand des Pseudonyms wiedererkennen können (auch "eingeschränkte Wiedererkennung" genannt).
Q
Qualifizierte Signaturkarten
Qualifizierte Signaturkarten ermöglichen dem Inhaber unter Anderem eine gemäß dem deutschen Signaturgesetz rechtskonforme elektronische Signatur , welche die Verbindlichkeit einer manuellen Unterschrift besitzt. Ein Paar der auf der qualifizierten Signaturkarte enthaltenen Schlüsselpaare sind durch ein von der Regulierungsbehörde für Post und Telekommunikation akkreditiertes Trustcenter eindeutig einem Inhaber zugeordnet und werden durch Produkte für qualifizierte Signaturen verarbeitet.
R
RC4
Nach seinem Entwickler Ronald L. Rivest benanntes, international anerkanntes Verfahren zur symmetrischen Verschlüsselung , bei dem Schlüssel unterschiedlicher Länge benutzt werden können. RC4 ist im Prinzip ein Pseudozufallsgenerator. Das Verfahren wurde 1987 von Rivest für das Unternehmen RSA Security entwickelt.
RSA-Verfahren
Der RSA-Algorithmus ist ein asymmetrisches, kryptographisches Verfahren und eignet sich zur elektronischen Signatur, Authentifizierung, sowie zum Schlüsselaustausch symmetrischer Schlüssel durch asymmetrische Verschlüsselung . Er wurde von Rivest, Shamir und Adleman 1977 entwickelt. Die Sicherheit dieses Algorithmus beruht vom Prinzip her auf der Schwierigkeit der Faktorisierung großer Zahlen.
S
Sicherheitscheck
Der Sicherheitscheck eines Systems kann formal oder technisch stattfinden. Es wird immer die Konfiguration des Systems hinsichtlich Unwägbarkeiten in Sachen Sicherheit überprüft, aus denen Empfehlungen zur Konfiguration des Computers resultieren. Weitere Informationen zur Sicherheit im Internet finden Sie auf der Seite von Deutschland sicher im Netz e. V.. Es gibt Softwareprodukte bzw. Scanner, welche die Sicherheitskonfiguration eines Computers prüfen. Es gibt hier Produkte, die auf dem Computer direkt ausgeführt werden müssen und Produkte, die über eine sichere Internet-Verbindung die Konfiguration des Computers prüfen.
Signaturgesetz
Das Signaturgesetz hat den Zweck, die Rahmenbedingungen für elektronische Signaturen zu schaffen, um dadurch die Rechtssicherheit zum Beispiel über das Internet getätigter Geschäfte zu erhöhen. Dieses Gesetz definiert die folgenden drei Arten von elektronischen Signaturen: Einfache elektronische Signaturen, fortgeschrittene elektronische Signaturen und qualifizierte elektronische Signaturen. Über die Einhaltung und Prüfung der Vorschriften in Bezug auf das Signaturgesetz wacht die Regulierungsbehörde für Telekommunikation und Post (Bundesnetzagentur).
Sperrlisten
Eine Sperrliste dient einem Trustcenter zur Veröffentlichung von Zertifikaten, die vor Ablauf ihrer Gültigkeit gesperrt wurden. Alle in einer Sperrliste aufgeführten Zertifikate sind ab dem Zeitpunkt der Publikation ungültig.
Secure Socket Layer (SSL)
Secure Socket Layer (SSL) ist ein Protokoll für sicheren Datenaustausch zwischen Computer und Server über das Internet. Computer und Server können sich mit Hilfe asymmetrischer kryptographischer Verfahren gegenseitig authentifizieren und die Daten beim Datenaustausch verschlüsseln. Entwickelt wurde dieses Protokoll von der Firma Netscape.
Symmetrische kryptographische Verfahren
Bei symmetrischen Verfahren wird derselbe geheime Schlüssel zur Verschlüsselung und Entschlüsselung von Daten verwendet. Soll die verschlüsselte Datei weitergeben werden, muss dem Empfänger der geheime Schlüssel auf einem sicheren Übertragungsweg mitgeteilt werden. Da es neben dem Gespräch unter vier Augen keine wirklich sichere Methode gibt, wird dies zum Problem. Asymmetrische Verfahren lösen das Problem des Schlüsselaustauschs.
T
TESTA
Bei TESTA (Trans-European Services for Telematics between Administrations) handelt es sich um ein Overlay-Netz der europäischen Verwaltungen. Das primäre Ziel von TESTA besteht darin, den europäischen Einrichtungen, Agenturen und Verwaltungen ein umfassendes, gut strukturiertes Dienstangebot auf der Basis anerkannter Marktstandards bereitzustellen, das einen einfachen und zuverlässigen Austausch von Daten ermöglicht und optimale Interoperabilität gewährleistet. Ein Teil dieses großen Projektes ist TESTA Deutschland, die Zusammenarbeit des Bundes und der Länder im Sinne eines Zusammenschlusses der einzelnen Landesnetze sowie dem direkten Anschluss einzelner Bundesbehörden und des Informationsverbundes Berlin-Bonn (IVBB). Das TESTA-Netz bildet damit das Rückgrat eines "Corporate Network Verwaltung" für die länderübergreifende Kommunikation.
Transport Layer Security (TLS)
Transport Layer Security (TLS) ist ein Protokoll für sicheren Datenaustausch zwischen Computer und Server über das Internet. Computer und Server können sich mit Hilfe asymmetrischer kryptographischer Verfahren gegenseitig authentifizieren und die Daten beim Datenaustausch verschlüsseln.
Trojaner
Eine scheinbar nützliche Datei beziehungsweise Software, die nicht den vermuteten Inhalt hat. Dadurch besteht die Möglichkeit für die Datei beziehungsweise Software, unbemerkt auf einem Computer nicht vorgesehene Funktionen zu installieren. Durch einen solchen Vorgang können beispielsweise Passwörter und andere vertrauliche Daten ausgespäht, verändert, gelöscht oder bei der nächsten Datenübertragung an einen Unberechtigten verschickt werden. Dieser "Datendiebstahl" bleibt ohne dedizierte Sicherheitsmechanismen in der Regel unbemerkt.
Trustcenter
Ein Trustcenter ist eine unabhängige, vertrauenswürdige Instanz, die für die Vergabe und die Verwaltung von elektronischen Zertifikaten zuständig ist. Das Trustcenter signiert die von ihm ausgestellten Zertifikate digital und garantiert somit für die Echtheit der Daten auf dem Zertifikat. Da bei asymmetrischen Verfahren alle Teilnehmer dem Trustcenter vertrauen, können sie auf diese Weise auch auf die Gültigkeit der ausgestellten Zertifikate und damit den öffentlichen Schlüsseln anderer Teilnehmer vertrauen.
V
Verschlüsselung
Unter Verschlüsselung versteht man die Transformation von Daten zu deren sicherer Aufbewahrung oder Übermittlung. Dazu wird mit Hilfe eines kryptographischen Schlüssels der Inhalt zum Beispiel eines Dokuments, einer Datei oder E-Mail für unbefugte Dritte unleserlich gemacht. Nur der richtige Empfänger kann die Daten mit Hilfe eines passenden (Entschlüsselungs-) Schlüssels wieder lesen. Es gibt unterschiedliche Verschlüsselungsverfahren wie symmetrische, asymmetrische und hybride Verschlüsselung.
Verzeichnisdienst
Verzeichnisdienst bezeichnet in diesem Dokument eine nach dem ITU-Standard X.500 hierarchisch (baumförmig) aufgebaute Datenbank, in der von einem geeigneten System aus Informationen abgerufen werden können. Anwendung findet dies zum Beispiel in Adress-, E-Mail- und Zertifikatsverzeichnissen, in denen nach unterschiedlichen Kriterien die gewünschte Information gesucht werden kann. Die Datenbank kann auch über mehrere Server verteilt vorliegen.
Virenscanner
Als Virenscanner wird eine Software bezeichnet, die durch das regelmäßige oder permanente Überprüfen von Dateien einen Computer (Computer, Server, ...) in gewissem Maße vor Computerviren schützt. Um optimalen Schutz zu gewährleisten, muss ein Virenscanner durch häufige und regelmäßige Updates der enthaltenen Virendefinitions-Dateien auf einem aktuellen Stand gehalten werden.
Vorausgefüllte Steuererklärung
Die vorausgefüllte Steuererklärung wird auch als Abruf von Bescheinigungen bezeichnet und ist ein kostenloses Serviceangebot der Steuerverwaltung. Diese elektronische Sammlung von Bescheinigungen hat das Ziel, Ihnen die Erstellung der Einkommensteuererklärung zu erleichtern. Die Steuerverwaltung sammelt für Sie Daten in elektronischer Form und stellt Ihnen diese Bescheinigungen zur Verfügung. Sie (oder ein von Ihnen Bevollmächtigter, z. B. Ihr Steuerberater) können so auf die zu Ihrer Person bei der Steuerverwaltung gespeicherten Informationen zugreifen und diese gegebenenfalls für Ihre Einkommensteuererklärung verwenden.
Als Bescheinigungen werden folgende elektronische Daten, die der Steuerverwaltung zu Ihrer Person übermittelt wurden, bezeichnet:
- vom Arbeitgeber übermittelte Lohnsteuerbescheinigungen
- Lohnersatzleistungen (zum Beispiel Arbeitslosengeld, Krankengeld, Elterngeld)
- Mitteilungen über den Bezug von Rentenleistungen
- Beiträge zu Kranken- und Pflegeversicherungen
- Vorsorgeaufwendungen (zum Beispiel Riester- oder Rürup-Verträge)
- Beiträge für Vermögenswirksame Leistungen (VWL / VL)
Z
Zertifikat
Ein elektronischer Ausweis für eine Person, Organisation beziehungsweise System, der von einem Trustcenter ausgestellt und durch dessen elektronische Signatur beglaubigt ist und insbesondere die Zuordnung eines öffentlichen Schlüssels zu einer Person, Organisation beziehungsweise einem System garantiert. Mein ELSTER stellt persönliche Zertifikate für Personen und Zertifikate für Organisationen (auch Organisationszertifikate) aus.